In order to recover a Windows NT/2000/XP administrator password that has been lost, one is required to have a local access to a machine. The first step is to boot the machine using a bootable floppy or CD which has the NTFS drivers. This enables one to proceed to the next step, which is to recover or reset the Administrator password.
Boot the system with NTFS drivers
There are several Linux-based boot disks with NTFS supports that are created by Petter Nordahl-Hagen. One can download this package from offline NT password and registry editor. One may also be able to use bootable floppies or CD’s as long as it supports NTFS file system and one can run the utility which one intends to use in order to recover the administrator password. This step is used only when the system uses the NTFS file system. If your system uses a different file system, then one has to use the drivers for that file system.
Recover the Administrator password
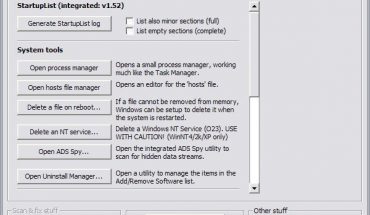
In order to recover the administrator password one can use a tool like L0phtCrack, or LCP by. John the Ripper runs on UNIX, DOS, or Windows, Open Wall’s John the Ripper with Olle Segerdahl’s NTLM patch. The L0phtCrack runs on UNIX or Windows and LCP runs on Microsoft Windows.
In order to reset the Administrator password one can use a tool like ‘chntpw; this is included with Petter Nordahl-Hagen’s boot disk package. One can gain access to the system after resetting the administrator. Once the password is reset one can log into the system without being a legitimate admin and one will know about the system admin password with which one can get access to the other machines.